41 min to read
OpenStack Mastery: Enterprise-Grade Cloud Infrastructure Guide
Complete guide to OpenStack architecture, deployment patterns, and production-ready implementation strategies
Understanding OpenStack
OpenStack stands as the cornerstone of modern enterprise cloud infrastructure, transforming how organizations build, deploy, and manage large-scale computing environments
As the world's most deployed open-source cloud platform, OpenStack enables enterprises to create sophisticated private and hybrid cloud infrastructures that rival the capabilities of public cloud providers while maintaining complete control over their data and operations.
In today's cloud-native landscape, organizations face increasing pressure to deliver infrastructure that can seamlessly scale from development environments to planet-scale production deployments while maintaining security, compliance, and cost-effectiveness.
OpenStack addresses these challenges through its distributed architecture, comprehensive service ecosystem, and enterprise-grade operational capabilities.
OpenStack addresses these challenges through its distributed architecture, comprehensive service ecosystem, and enterprise-grade operational capabilities.
This comprehensive guide explores OpenStack from foundational concepts to enterprise-grade production patterns, covering advanced deployment strategies, performance optimization techniques, security implementations, and operational excellence practices.
The Enterprise Cloud Operating System
OpenStack transcends traditional virtualization platforms by providing a complete cloud operating system that orchestrates compute, storage, and networking resources across distributed environments with unprecedented sophistication.
Modern Cloud Architecture Principles
- Infrastructure as a Service (IaaS): Complete virtualized computing resources with programmatic control
- API-First Design: All functions accessible through RESTful APIs enabling automation and integration
- Microservices Architecture: Modular, loosely-coupled services that can be deployed and scaled independently
- Multi-Tenancy: Secure isolation between tenants with granular resource allocation and access control
- Horizontal Scalability: Designed to scale across thousands of nodes in distributed deployments
OpenStack Architecture Overview (Diagram Description)
- OpenStack Cloud Platform
- Compute (Nova)
- Storage (Cinder, Swift)
- Networking (Neutron)
- Identity (Keystone)
- Dashboard (Horizon)
- Additional Services (Heat, Ceilometer, Trove)
Enterprise Architecture Deep Dive
OpenStack’s distributed architecture represents a masterclass in cloud service design, balancing scalability, reliability, and performance through carefully orchestrated components. Understanding this architecture is fundamental to deploying, operating, and optimizing OpenStack in production environments.
Core Service Components Deep Dive
Nova (Compute Service): The Heart of Cloud Infrastructure
Nova orchestrates the complete lifecycle of compute instances, from initial placement decisions through complex migration scenarios, while supporting diverse workloads from simple web applications to high-performance computing clusters.
# Enterprise Nova Configuration
[DEFAULT]
# High availability configuration
my_ip = 10.0.0.31
use_neutron = true
firewall_driver = nova.virt.firewall.NoopFirewallDriver
# Advanced compute configuration
cpu_allocation_ratio = 16.0
ram_allocation_ratio = 1.5
disk_allocation_ratio = 1.0
# Instance configuration
instances_path = /var/lib/nova/instances
instance_usage_audit = true
instance_usage_audit_period = hour
[api_database]
connection = mysql+pymysql://nova:NOVA_PASS@controller/nova_api
[database]
connection = mysql+pymysql://nova:NOVA_PASS@controller/nova
[oslo_messaging_rabbit]
rabbit_hosts = controller1:5672,controller2:5672,controller3:5672
rabbit_retry_interval = 1
rabbit_retry_backoff = 2
rabbit_max_retries = 0
rabbit_ha_queues = true
[keystone_authtoken]
# Authentication configuration
www_authenticate_uri = http://controller:5000/
auth_url = http://controller:5000/
memcached_servers = controller1:11211,controller2:11211,controller3:11211
auth_type = password
project_domain_name = Default
user_domain_name = Default
project_name = service
username = nova
password = NOVA_PASS
[vnc]
enabled = true
server_listen = $my_ip
server_proxyclient_address = $my_ip
[glance]
api_servers = http://controller:9292
[oslo_concurrency]
lock_path = /var/lib/nova/tmp
[placement]
region_name = RegionOne
project_domain_name = Default
project_name = service
auth_type = password
user_domain_name = Default
auth_url = http://controller:5000/v3
username = placement
password = PLACEMENT_PASS
[libvirt]
# Advanced virtualization settings
virt_type = kvm
cpu_mode = host-passthrough
disk_cachemodes = file=directsync,block=none
# NUMA topology awareness
cpu_dedicated_set = 2-23,26-47
cpu_shared_set = 0-1,24-25
# Live migration configuration
live_migration_uri = qemu+ssh://nova@%s/system
live_migration_tunnelled = false
live_migration_with_native_luks = false
# Performance optimization
use_virtio_for_bridges = true
vif_plugging_timeout = 300
vif_plugging_is_fatal = false
Neutron (Networking): Software-Defined Networking at Scale
Neutron provides comprehensive networking capabilities including advanced routing, load balancing, VPN services, and microsegmentation for complex enterprise network topologies.
# Enterprise Neutron Configuration
[DEFAULT]
core_plugin = ml2
service_plugins = router,lbaasv2,vpnaas,firewall_v2,qos
# High availability
dhcp_agents_per_network = 3
max_l3_agents_per_router = 3
l3_ha = true
l3_ha_net_cidr = 169.254.192.0/18
[database]
connection = mysql+pymysql://neutron:NEUTRON_PASS@controller/neutron
[keystone_authtoken]
www_authenticate_uri = http://controller:5000
auth_url = http://controller:5000
memcached_servers = controller1:11211,controller2:11211,controller3:11211
auth_type = password
project_domain_name = Default
user_domain_name = Default
project_name = service
username = neutron
password = NEUTRON_PASS
[nova]
auth_url = http://controller:5000
auth_type = password
project_domain_name = Default
user_domain_name = Default
region_name = RegionOne
project_name = service
username = nova
password = NOVA_PASS
[ml2]
type_drivers = flat,vlan,vxlan,gre
tenant_network_types = vxlan
mechanism_drivers = openvswitch,l2population
extension_drivers = port_security,qos
[ml2_type_vxlan]
vni_ranges = 1:1000
[securitygroup]
firewall_driver = neutron.agent.linux.iptables_firewall.OVSHybridIptablesFirewallDriver
Cinder (Block Storage): Enterprise Storage Management
Cinder provides persistent block storage with advanced features including snapshots, backups, replication, and integration with enterprise storage systems.
# Enterprise Cinder Configuration
[DEFAULT]
# Storage backend configuration
enabled_backends = ceph-ssd,ceph-hdd,nfs-backup
default_volume_type = ceph-ssd
# Performance optimization
osapi_volume_workers = 8
volume_clear = zero
volume_clear_size = 0
[database]
connection = mysql+pymysql://cinder:CINDER_PASS@controller/cinder
[keystone_authtoken]
www_authenticate_uri = http://controller:5000
auth_url = http://controller:5000
memcached_servers = controller1:11211,controller2:11211,controller3:11211
auth_type = password
project_domain_name = Default
user_domain_name = Default
project_name = service
username = cinder
password = CINDER_PASS
# Ceph SSD backend
[ceph-ssd]
volume_driver = cinder.volume.drivers.rbd.RBDDriver
volume_backend_name = ceph-ssd
rbd_pool = volumes-ssd
rbd_ceph_conf = /etc/ceph/ceph.conf
rbd_flatten_volume_from_snapshot = false
rbd_max_clone_depth = 5
rbd_store_chunk_size = 4
rados_connect_timeout = -1
rbd_user = cinder
rbd_secret_uuid = 457eb676-33da-42ec-9a8c-9293d545c337
# Ceph HDD backend for archives
[ceph-hdd]
volume_driver = cinder.volume.drivers.rbd.RBDDriver
volume_backend_name = ceph-hdd
rbd_pool = volumes-hdd
rbd_ceph_conf = /etc/ceph/ceph.conf
rbd_user = cinder
rbd_secret_uuid = 457eb676-33da-42ec-9a8c-9293d545c337
# NFS backup backend
[nfs-backup]
volume_driver = cinder.volume.drivers.nfs.NfsDriver
volume_backend_name = nfs-backup
nfs_shares_config = /etc/cinder/nfs_shares
nfs_mount_point_base = /var/lib/cinder/nfs
Advanced Service Integration Patterns
Message Queue Architecture for High Availability
OpenStack’s asynchronous communication relies on a sophisticated message queue system that ensures reliable delivery and fault tolerance across distributed deployments.
# RabbitMQ Cluster Configuration
[oslo_messaging_rabbit]
# Cluster configuration for high availability
rabbit_hosts = rabbit1:5672,rabbit2:5672,rabbit3:5672
rabbit_use_ssl = true
rabbit_userid = openstack
rabbit_password = RABBIT_PASS
rabbit_virtual_host = /
rabbit_ha_queues = true
rabbit_heartbeat_timeout_threshold = 60
rabbit_heartbeat_rate = 3
rabbit_retry_interval = 1
rabbit_retry_backoff = 2
rabbit_max_retries = 0
# Advanced messaging features
kombu_missing_consumer_retry_timeout = 60
kombu_failover_strategy = round-robin
kombu_compression = gzip
# Message durability and reliability
rabbit_durable_queues = true
rabbit_queue_ttl = 0
amqp_auto_delete = false
Database Clustering and Performance Optimization
# Galera Cluster Configuration for Database High Availability
[database]
# Master database connection
connection = mysql+pymysql://openstack:DB_PASS@vip-db/openstack?charset=utf8
# Read replica configuration for performance
slave_connection = mysql+pymysql://openstack:DB_PASS@vip-db-ro/openstack?charset=utf8
# Connection pool optimization
max_pool_size = 50
max_overflow = 100
pool_timeout = 30
pool_recycle = 3600
pool_pre_ping = true
# Performance tuning
max_retries = -1
retry_interval = 10
Supporting Services and Advanced Features
Heat (Orchestration): Infrastructure as Code
Heat provides sophisticated template-based orchestration capabilities for complex multi-tier application deployments.
# Advanced Heat Template Example
heat_template_version: 2018-08-31
description: >
Enterprise 3-tier application deployment with auto-scaling,
load balancing, and monitoring integration
parameters:
key_name:
type: string
description: SSH key pair name
instance_flavor:
type: string
default: m1.medium
description: Instance flavor for application servers
min_cluster_size:
type: number
default: 2
description: Minimum number of application servers
max_cluster_size:
type: number
default: 10
description: Maximum number of application servers
resources:
# Load balancer configuration
web_loadbalancer:
type: OS::Octavia::LoadBalancer
properties:
vip_subnet: { get_resource: private_subnet }
name: web-lb
# Auto-scaling group
web_server_group:
type: OS::Heat::AutoScalingGroup
properties:
min_size: { get_param: min_cluster_size }
max_size: { get_param: max_cluster_size }
resource:
type: web_server.yaml
properties:
flavor: { get_param: instance_flavor }
key_name: { get_param: key_name }
subnet: { get_resource: private_subnet }
security_group: { get_resource: web_security_group }
# Scaling policies
scale_up_policy:
type: OS::Heat::ScalingPolicy
properties:
adjustment_type: change_in_capacity
auto_scaling_group_id: { get_resource: web_server_group }
cooldown: 300
scaling_adjustment: 1
# CloudWatch-style alarms
cpu_alarm_high:
type: OS::Ceilometer::Alarm
properties:
description: High CPU utilization alarm
meter_name: cpu_util
statistic: avg
period: 300
evaluation_periods: 2
threshold: 80
comparison_operator: gt
alarm_actions:
- { get_attr: [scale_up_policy, alarm_url] }
Barbican (Key Management): Enterprise Security
Barbican provides centralized key management and certificate services for enterprise security requirements.
# Barbican Enterprise Configuration
[DEFAULT]
# Core configuration
bind_host = 0.0.0.0
bind_port = 9311
host_href = https://barbican.example.com:9311
backlog = 4096
max_allowed_secret_in_bytes = 10000
max_allowed_request_size_in_bytes = 1000000
[secretstore]
namespace = barbican.secretstore.plugin
enabled_secretstore_plugins = store_crypto
[crypto]
namespace = barbican.crypto.plugin
enabled_crypto_plugins = p11_crypto
# Hardware Security Module integration
[p11_crypto_plugin]
# PKCS#11 configuration for HSM
library_path = /usr/lib/libCryptoki2_64.so
login = password
mkek_label = mkek
mkek_length = 32
hmac_label = hmac
slot_id = 1
[certificate]
namespace = barbican.certificate.plugin
enabled_certificate_plugins = snakeoil_ca,dogtag_ca
[dogtag_ca_plugin]
# Integration with enterprise CA
dogtag_host = ca.example.com
dogtag_port = 8443
nss_db_path = /etc/barbican/alias
nss_password = barbican_nss_password
Getting Started with Enterprise OpenStack
Modern OpenStack adoption requires a strategic approach that considers both immediate deployment needs and long-term scalability requirements. This section provides guidance for organizations embarking on their OpenStack journey.
Strategic Deployment Roadmap
| Phase | Objectives | Key Activities |
|---|---|---|
| Phase 1: Foundation (Months 1-3) |
|
|
| Phase 2: Enhancement (Months 4-8) |
|
|
| Phase 3: Scale (Months 9-12) |
|
|
Production-Grade Deployment Script
Enterprise Success Patterns and Best Practices
Implementation Considerations
| Strategic Advantages | Implementation Challenges |
|---|---|
|
|
Enterprise Use Cases and Success Stories
Telecommunications and Edge Computing
- 5G Network Function Virtualization: Telecom operators deploying cloud-native network functions
- Edge Computing Platforms: Distributed OpenStack deployments for low-latency applications
- Multi-Access Edge Computing: Integration with 5G infrastructure for edge services
Financial Services and Compliance
- Regulatory Compliance: HIPAA, SOX, PCI-DSS compliant private cloud infrastructure
- High-Frequency Trading: Ultra-low latency compute infrastructure for financial markets
- Data Sovereignty: Complete control over sensitive financial data and operations
Scientific Research and HPC
- Large Hadron Collider: CERN’s massive OpenStack deployment for particle physics research
- Weather Modeling: National weather services using OpenStack for climate simulations
- Genomics Research: Scalable compute infrastructure for bioinformatics workloads
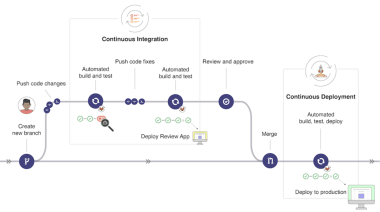
Architectural Overview
- Users/API Clients → API Gateway → Identity Service (Keystone)
- API Gateway → Dashboard (Horizon)
- API Gateway → Compute (Nova) → Hypervisors
- API Gateway → Networking (Neutron) → Network Infrastructure
- API Gateway → Block Storage (Cinder) → Storage Backend
- API Gateway → Object Storage (Swift) → Object Storage Nodes
- API Gateway → Image Service (Glance) → Image Repository
- API Gateway → Orchestration (Heat)
- All major services interact with Message Queue and Database for coordination and state.
Enterprise Deployment Strategies and Production Patterns
Modern OpenStack deployments require sophisticated deployment strategies that address high availability, disaster recovery, performance optimization, and operational excellence across distributed infrastructure.
Advanced High Availability Architecture
Multi-Region Active-Active Deployment
# Global OpenStack Architecture
global_architecture:
regions:
us_east_1:
availability_zones:
- us-east-1a
- us-east-1b
- us-east-1c
controllers: 3
compute_nodes: 50
storage_nodes: 12
us_west_1:
availability_zones:
- us-west-1a
- us-west-1b
- us-west-1c
controllers: 3
compute_nodes: 30
storage_nodes: 8
eu_west_1:
availability_zones:
- eu-west-1a
- eu-west-1b
- eu-west-1c
controllers: 3
compute_nodes: 40
storage_nodes: 10
shared_services:
keystone_federation:
type: saml
identity_providers:
- active_directory
- okta
- google_workspace
global_load_balancer:
type: f5_bigip
endpoints:
- region: us_east_1
weight: 40
- region: us_west_1
weight: 30
- region: eu_west_1
weight: 30
backup_strategy:
type: cross_region
replication_frequency: hourly
retention_policy: 90_days
Advanced Load Balancing and API Gateway
# HAProxy Configuration for OpenStack APIs
[DEFAULT]
# Global configuration
daemon
maxconn 4096
log stdout local0
user haproxy
group haproxy
stats socket /var/run/haproxy.sock mode 600 level admin
defaults:
mode http
log global
option httplog
option dontlognull
option redispatch
timeout connect 5000ms
timeout client 50000ms
timeout server 50000ms
errorfile 400 /etc/haproxy/errors/400.http
errorfile 403 /etc/haproxy/errors/403.http
errorfile 408 /etc/haproxy/errors/408.http
errorfile 500 /etc/haproxy/errors/500.http
errorfile 502 /etc/haproxy/errors/502.http
errorfile 503 /etc/haproxy/errors/503.http
errorfile 504 /etc/haproxy/errors/504.http
# API Gateway configuration
frontend openstack_api_gateway
bind *:443 ssl crt /etc/ssl/certs/openstack.pem
mode http
option httplog
# Rate limiting
stick-table type ip size 100k expire 30s store http_req_rate(10s)
http-request track-sc0 src
http-request reject if { sc_http_req_rate(0) gt 20 }
# Service routing based on URL path
acl nova_api path_beg /compute
acl neutron_api path_beg /network
acl cinder_api path_beg /volume
acl glance_api path_beg /image
acl keystone_api path_beg /identity
use_backend nova_servers if nova_api
use_backend neutron_servers if neutron_api
use_backend cinder_servers if cinder_api
use_backend glance_servers if glance_api
use_backend keystone_servers if keystone_api
# Backend server pools
backend nova_servers
balance roundrobin
option httpchk GET /
server controller1 10.0.0.11:8774 check
server controller2 10.0.0.12:8774 check
server controller3 10.0.0.13:8774 check
backend neutron_servers
balance roundrobin
option httpchk GET /
server controller1 10.0.0.11:9696 check
server controller2 10.0.0.12:9696 check
server controller3 10.0.0.13:9696 check
Performance Optimization and Hardware Acceleration
NUMA-Aware Resource Allocation
Modern enterprise workloads require sophisticated NUMA topology awareness for optimal performance.
# Advanced NUMA Configuration
[libvirt]
# CPU topology configuration
cpu_dedicated_set = 2-23,26-47 # Dedicated cores for VMs
cpu_shared_set = 0-1,24-25 # Shared cores for infrastructure
# NUMA-aware scheduling
cpu_mode = host-passthrough
cpu_model_extra_flags = pcid
# Memory optimization
mem_stats_period_seconds = 0
remove_unused_base_images = true
remove_unused_original_minimum_age_seconds = 86400
# Huge pages configuration
[compute]
cpu_shared_set = 0-1,24-25
cpu_dedicated_set = 2-23,26-47
# Flavor configuration for NUMA-aware instances
flavor_extra_specs = {
'hw:numa_nodes': '2',
'hw:numa_cpus.0': '0-11',
'hw:numa_cpus.1': '12-23',
'hw:numa_mem.0': '8192',
'hw:numa_mem.1': '8192',
'hw:cpu_thread_policy': 'prefer',
'hw:mem_page_size': '1GB'
}
SR-IOV and Hardware Acceleration
# SR-IOV Configuration for High-Performance Networking
[pci]
# SR-IOV device configuration
passthrough_whitelist = [
{
"devname": "p4p1",
"physical_network": "physnet1"
},
{
"devname": "p4p2",
"physical_network": "physnet2"
}
]
# PCI alias for GPU passthrough
alias = {
"nvidia-v100": {
"vendor_id": "10de",
"product_id": "1db4",
"device_type": "type-PCI"
},
"intel-fpga": {
"vendor_id": "8086",
"product_id": "0b30",
"device_type": "type-PCI"
}
}
[neutron]
# SR-IOV agent configuration
physical_device_mappings = physnet1:p4p1,physnet2:p4p2
exclude_devices =
[ml2_sriov]
# Neutron SR-IOV configuration
supported_pci_vendor_devs = 15b3:1004,8086:10ed,8086:1515
agent_required = true
Security and Compliance Framework
Enterprise OpenStack deployments require comprehensive security measures addressing multi-tenancy, compliance requirements, and threat protection across the entire infrastructure stack.
Advanced Security Architecture
# Enterprise Security Configuration
[DEFAULT]
# Security hardening
secure_proxy_ssl_header = HTTP_X_FORWARDED_PROTO
secure_proxy_ssl_header_value = https
use_ssl = true
ssl_cert_file = /etc/ssl/certs/openstack.crt
ssl_key_file = /etc/ssl/private/openstack.key
ssl_ca_file = /etc/ssl/certs/ca-bundle.crt
# Audit logging
notification_driver = messagingv2
notification_topics = notifications
notify_on_state_change = vm_and_task_state
[keystone_authtoken]
# Enhanced authentication
auth_version = v3
interface = internal
region_name = RegionOne
memcache_security_strategy = ENCRYPT
memcache_secret_key = SECRET_KEY
token_cache_time = 300
# Multi-factor authentication support
mfa_rules = [
{
"ID": "admin_mfa",
"local": [
{
"user": {
"name": "{0}",
"domain": {"name": "Default"}
}
}
],
"remote": [
{
"type": "OIDC-preferred_username"
}
]
}
]
[cors]
# Cross-origin resource sharing
allowed_origin = https://dashboard.example.com
allow_credentials = true
expose_headers = Content-Type,Cache-Control,Content-Language,Expires,Last-Modified,Pragma
max_age = 3600
[oslo_messaging_notifications]
# Secure messaging
driver = messagingv2
transport_url = rabbit://openstack:RABBIT_PASS@controller1:5672,openstack:RABBIT_PASS@controller2:5672,openstack:RABBIT_PASS@controller3:5672/openstack
topics = notifications
Network Security and Microsegmentation
# Advanced Security Groups and Network Policies
security_group_rules = [
{
"direction": "ingress",
"ethertype": "IPv4",
"protocol": "tcp",
"port_range_min": 22,
"port_range_max": 22,
"remote_ip_prefix": "10.0.0.0/8",
"description": "SSH access from management network"
},
{
"direction": "ingress",
"ethertype": "IPv4",
"protocol": "tcp",
"port_range_min": 443,
"port_range_max": 443,
"remote_group_id": "web-tier-sg",
"description": "HTTPS from web tier"
},
{
"direction": "egress",
"ethertype": "IPv4",
"protocol": "tcp",
"port_range_min": 3306,
"port_range_max": 3306,
"remote_group_id": "db-tier-sg",
"description": "MySQL to database tier"
}
]
# Network ACLs for additional security layers
network_acl_rules = [
{
"action": "allow",
"destination_ip_prefix": "192.168.1.0/24",
"destination_port_range_max": 80,
"destination_port_range_min": 80,
"enabled": True,
"ip_version": 4,
"protocol": "tcp",
"source_ip_prefix": "10.0.0.0/8"
}
]
Monitoring, Observability, and Operational Excellence
Comprehensive Monitoring Stack
# Prometheus Configuration for OpenStack Monitoring
global:
scrape_interval: 15s
evaluation_interval: 15s
rule_files:
- "openstack_alerts.yml"
scrape_configs:
# OpenStack service monitoring
- job_name: 'openstack-nova'
static_configs:
- targets: ['controller1:8774', 'controller2:8774', 'controller3:8774']
metrics_path: /metrics
scrape_interval: 30s
- job_name: 'openstack-neutron'
static_configs:
- targets: ['controller1:9696', 'controller2:9696', 'controller3:9696']
metrics_path: /metrics
scrape_interval: 30s
# Infrastructure monitoring
- job_name: 'node-exporter'
static_configs:
- targets: ['controller1:9100', 'controller2:9100', 'controller3:9100']
- targets: ['compute1:9100', 'compute2:9100', 'compute3:9100']
scrape_interval: 15s
# Database monitoring
- job_name: 'mysqld-exporter'
static_configs:
- targets: ['db1:9104', 'db2:9104', 'db3:9104']
scrape_interval: 30s
alerting:
alertmanagers:
- static_configs:
- targets:
- alertmanager1:9093
- alertmanager2:9093
- alertmanager3:9093
Intelligent Alerting and Automation
Production-Ready Deployment Patterns
Enterprise OpenStack deployments require sophisticated automation and lifecycle management approaches that can handle complex multi-site environments while maintaining operational consistency and reliability.
Container-Based Deployment with Kolla-Ansible
Modern OpenStack deployments leverage containerization for improved consistency, easier upgrades, and better resource isolation.
# Advanced Kolla-Ansible Configuration
[DEFAULT]
# Global deployment configuration
enable_openstack_core = "yes"
enable_glance = "yes"
enable_nova = "yes"
enable_neutron = "yes"
enable_cinder = "yes"
enable_heat = "yes"
enable_horizon = "yes"
# Advanced services
enable_barbican = "yes"
enable_octavia = "yes"
enable_magnum = "yes"
enable_manila = "yes"
enable_designate = "yes"
# High availability configuration
enable_haproxy = "yes"
enable_keepalived = "yes"
enable_mariadb = "yes"
enable_memcached = "yes"
enable_rabbitmq = "yes"
# Monitoring and logging
enable_prometheus = "yes"
enable_grafana = "yes"
enable_elasticsearch = "yes"
enable_kibana = "yes"
enable_fluentd = "yes"
# Network configuration
network_interface = "eth0"
neutron_external_interface = "eth1"
neutron_plugin_agent = "openvswitch"
enable_neutron_dvr = "yes"
enable_neutron_qos = "yes"
# Storage configuration
enable_cinder_backup = "yes"
cinder_backup_driver = "swift"
enable_swift = "yes"
swift_storage_interface = "eth2"
# Security configuration
keystone_token_provider = "fernet"
keystone_fernet_token_expiry = 21600
enable_barbican_simple_crypto = "yes"
# Performance optimization
openstack_logging_debug = "False"
nova_compute_virt_type = "kvm"
nova_safety_upgrade = "yes"
# Resource allocation
openstack_release = "2024.1"
kolla_base_distro = "ubuntu"
kolla_install_type = "source"
Infrastructure as Code with Heat Templates
# Enterprise Application Stack Template
heat_template_version: 2021-04-16
description: >
Production-grade multi-tier application deployment with
auto-scaling, monitoring, and disaster recovery capabilities
parameters:
environment:
type: string
default: production
constraints:
- allowed_values: [development, staging, production]
application_tier_min_size:
type: number
default: 3
description: Minimum number of application servers
application_tier_max_size:
type: number
default: 20
description: Maximum number of application servers
database_tier_size:
type: number
default: 3
description: Number of database servers
availability_zones:
type: comma_delimited_list
default: ["az1", "az2", "az3"]
description: List of availability zones
resources:
# Network infrastructure
private_network:
type: OS::Neutron::Net
properties:
name: { str_replace: { template: "%env%-private-network", params: { "%env%": { get_param: environment } } } }
admin_state_up: true
private_subnet:
type: OS::Neutron::Subnet
properties:
network: { get_resource: private_network }
cidr: "192.168.100.0/24"
gateway_ip: "192.168.100.1"
dns_nameservers: ["8.8.8.8", "8.8.4.4"]
allocation_pools:
- start: "192.168.100.10"
end: "192.168.100.200"
# Load balancer for high availability
application_loadbalancer:
type: OS::Octavia::LoadBalancer
properties:
vip_subnet: { get_resource: private_subnet }
name: { str_replace: { template: "%env%-app-lb", params: { "%env%": { get_param: environment } } } }
lb_pool:
type: OS::Octavia::Pool
properties:
lb_algorithm: ROUND_ROBIN
protocol: HTTP
loadbalancer: { get_resource: application_loadbalancer }
# Auto-scaling application tier
application_cluster:
type: OS::Heat::AutoScalingGroup
properties:
min_size: { get_param: application_tier_min_size }
max_size: { get_param: application_tier_max_size }
desired_capacity: { get_param: application_tier_min_size }
resource:
type: application_server.yaml
properties:
flavor: "m1.large"
image: "ubuntu-20.04-app"
key_name: { get_param: key_name }
network: { get_resource: private_network }
subnet: { get_resource: private_subnet }
security_group: { get_resource: app_security_group }
lb_pool: { get_resource: lb_pool }
# Database cluster
database_cluster:
type: OS::Heat::ResourceGroup
properties:
count: { get_param: database_tier_size }
resource_def:
type: database_server.yaml
properties:
flavor: "db1.large"
image: "ubuntu-20.04-mysql"
key_name: { get_param: key_name }
network: { get_resource: private_network }
subnet: { get_resource: private_subnet }
security_group: { get_resource: db_security_group }
availability_zone: { get_param: [availability_zones, "%index%"] }
# Monitoring and alerting
monitoring_server:
type: OS::Nova::Server
properties:
name: { str_replace: { template: "%env%-monitoring", params: { "%env%": { get_param: environment } } } }
flavor: "m1.medium"
image: "ubuntu-20.04-monitoring"
key_name: { get_param: key_name }
networks:
- network: { get_resource: private_network }
security_groups:
- { get_resource: monitoring_security_group }
user_data:
str_replace:
template: |
#!/bin/bash
# Install and configure monitoring stack
apt-get update
apt-get install -y prometheus grafana alertmanager
# Configure Prometheus targets
cat > /etc/prometheus/prometheus.yml << EOF
global:
scrape_interval: 15s
scrape_configs:
- job_name: 'application-servers'
static_configs:
- targets: $app_targets
- job_name: 'database-servers'
static_configs:
- targets: $db_targets
EOF
systemctl enable prometheus grafana-server alertmanager
systemctl start prometheus grafana-server alertmanager
params:
$app_targets: { get_attr: [application_cluster, outputs_list, server_ip] }
$db_targets: { get_attr: [database_cluster, outputs, server_ip] }
outputs:
load_balancer_ip:
description: Load balancer VIP address
value: { get_attr: [application_loadbalancer, vip_address] }
application_servers:
description: List of application server IPs
value: { get_attr: [application_cluster, outputs_list, server_ip] }
database_servers:
description: List of database server IPs
value: { get_attr: [database_cluster, outputs, server_ip] }
monitoring_dashboard:
description: Monitoring dashboard URL
value:
str_replace:
template: "http://%server_ip%:3000"
params:
"%server_ip%": { get_attr: [monitoring_server, first_address] }
Getting Started with OpenStack
For those interested in exploring OpenStack, there are several approaches to get started—from simple development environments to full production deployments. The right approach depends on your goals and available resources.
Deployment Options
| Method | Description | Best For |
|---|---|---|
| DevStack |
|
|
| Packstack |
|
|
| Kolla-Ansible |
|
|
| TripleO |
|
|
Basic DevStack Setup
Key Points
-
Enterprise Architecture
- Distributed, scalable architecture supporting thousands of nodes
- Advanced service integration with comprehensive API ecosystem
- Production-ready deployment patterns with high availability
- Container-based deployment for operational excellence -
Advanced Capabilities
- NUMA-aware scheduling and hardware acceleration support
- Comprehensive security framework with enterprise integration
- Multi-region deployment with disaster recovery
- Infrastructure as Code with Heat orchestration
- Advanced monitoring and observability stack -
Production Excellence
- Strategic deployment roadmap for enterprise adoption
- Performance optimization for demanding workloads
- Compliance and governance frameworks
- Operational automation and lifecycle management
- Cost optimization and vendor independence -
Enterprise Integration
- LDAP/Active Directory integration for identity management
- Multi-tenant security with role-based access control
- Integration with existing enterprise infrastructure
- Support for specialized hardware and accelerators
- Comprehensive audit and compliance capabilities
Conclusion
OpenStack represents the pinnacle of enterprise cloud infrastructure technology, offering organizations the power to build and operate sophisticated cloud platforms that rival the capabilities of public cloud providers while maintaining complete control over their infrastructure and data.
The journey to OpenStack mastery requires significant investment in expertise, infrastructure, and operational processes. However, organizations that successfully implement OpenStack gain unprecedented control over their cloud destiny, enabling innovation, cost optimization, and competitive advantage in an increasingly cloud-native world.
From telecommunications companies deploying 5G infrastructure to financial institutions managing sensitive data, from research organizations processing massive datasets to government agencies maintaining sovereignty over critical systems, OpenStack continues to power the world’s most demanding enterprise workloads.
Success with OpenStack demands a strategic approach that balances immediate deployment needs with long-term scalability requirements, comprehensive technical expertise with operational excellence, and innovation velocity with stability and security.
As cloud computing continues to evolve toward hybrid and multi-cloud architectures, OpenStack’s role as the foundation for private and hybrid cloud deployments becomes increasingly critical, providing the consistency, control, and capabilities that enterprise organizations require for their most important workloads.
References
- OpenStack Documentation
- OpenStack Foundation
- OpenStack Wiki
- OpenStack Architecture Design Guide
- OpenStack Security Guide
- OpenStack Operations Guide
- Kolla-Ansible Documentation
- OpenStack Heat Documentation
- OpenStack Barbican Documentation
- OpenStack Placement Documentation
- OpenStack Performance and Optimization Guide

Comments